Recently identified is a memory corruption vulnerability in GNU Glibc that leaves smart vehicles open to penetration, warns Cisco’s Customer Experience Assessment & Penetration Team (CX APT).
The vulnerability in GNU libc for ARMv7 was found during recent research from Cisco’s Customer Experience Assessment & Penetration Team (CX APT).
Exploitation
So, it leaves Linux ARMv7 systems open to exploitation, & this vulnerability is identified as TALOS-2020-1019/CVE-2020-6096.
Security threats & cyber-attacks on ‘exposed connected vehicles’ can also produce software vulnerabilities, attacks based on hardware &, according to a Talos Intelligence blog, could even ‘remote control’ a vehicle.
It is now a truism that cars can be defined complex machines that merge both mechanical & computer systems.
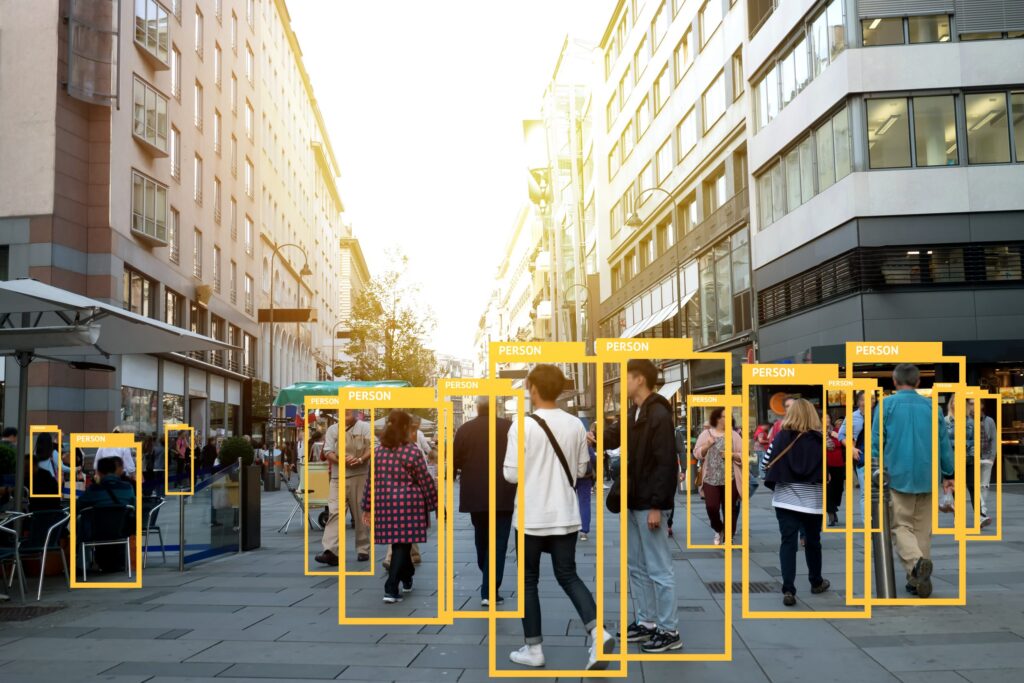
More sensors & devices are helping cars to measure & understand its external & internal location, temperature & other environmental matters, as well as distance from other things.
Sensors
This report explained “These sensors provide drivers with real-time information, connect the vehicle to the global fleet network &, in some cases, actively use and interpret this telemetry data to drive the vehicle.”
The latest generation of cars can merge both mobile & cloud components to improve driver experience, including ‘over the air updates’, ‘remote start-stop’ & monitoring.
These systems introduce a lot of “different attack vectors” in vehicles that are connected through mobile networks, WiFI, Bluetooth, DAB, USB, the report went on to say.
Vulnerability
Andrew Tierney of Pen Test Partners commented that the vulnerability was larger than just vehicles & would involve the IoT more generally.
“While it’s an interesting bug that we are surprised hasn’t been spotted before, we don’t see why Talos are highlighting this as a ‘vehicle’ issue, Tierney observed with puzzlement.
“While it is true that more than 90% of vehicle IVIs (sat nav head units) are ARM / Linux based & therefore might be vulnerable in some configurations, this issue affects a wide swathe of IoT & other embedded systems including industrial controls.
Embedded
“This is a significant security flaw that affects IoT, not just cars. While vehicle OEMs may be quick to address this, we fear that many older & possibly unsupported embedded systems will never be patched.
“This is a vulnerability for IoT and ICS hackers to dine out on for years to come.”
Giving technical details, the report went on to say “The CX APT IoT security practice specialises in identifying vulnerabilities in connected vehicle components.
“CX APT worked with Cisco Talos to disclose the vulnerability & the libc library maintainers plan to release an update that fixes this vulnerability in August.”
Science-fiction
Will reality catch up with Science-fiction before too long in order to compromise the very cars that we drive?
https://www.cybernewsgroup.co.uk/virtual-conferences/