An API bug exposed personal information of users such as political leanings, astrological signs, education, & even height & weight, & their distance away in miles.
After a taking closer look at the code for popular dating site & app Bumble, where women typically initiate the conversation, Independent Security Evaluators researcher Sanjana Sarda found concerning API vulnerabilities.
These not only allowed her to bypass paying for ‘Bumble Boost’ premium services, but she also was able to access personal information for the platform’s entire user base of nearly 100m.
Easy
Sarda suggested these issues were easy to find, & that the company’s response to her report on the flaws shows that Bumble needs to take testing & vulnerability disclosure more seriously.
Hacker One, the platform that hosts Bumble’s bug-bounty & reporting process, commented that the romancing service actually has a good history of collaborating with ethical hackers.
Bug
“It took me approximately 2 days to find the initial vulnerabilities & about 2 more days to come up with a proofs-of- concept for further exploits based on the same vulnerabilities,” Sarda explained. “Although API issues are not as well-known as something like SQL injection, these issues can cause significant damage.”
She reverse-engineered Bumble’s API & found several endpoints that were processing actions without being checked by the server.
Web Application
That meant that the limits on premium services, like the total number of positive “right” swipes per day allowed (swiping right means you’re interested in the potential match), were simply ‘bypassed’ by using Bumble’s web application the mobile instead of version.
Another premium-tier service from Bumble Boost is called ‘The Beeline’, which lets users see all the people who have swiped right on their profile. Here, Sarda explained that she used the Developer Console to find an endpoint that displayed every user in a potential match feed.
She was then able to work out the codes for those who swiped right, & those who did not.
Accessible
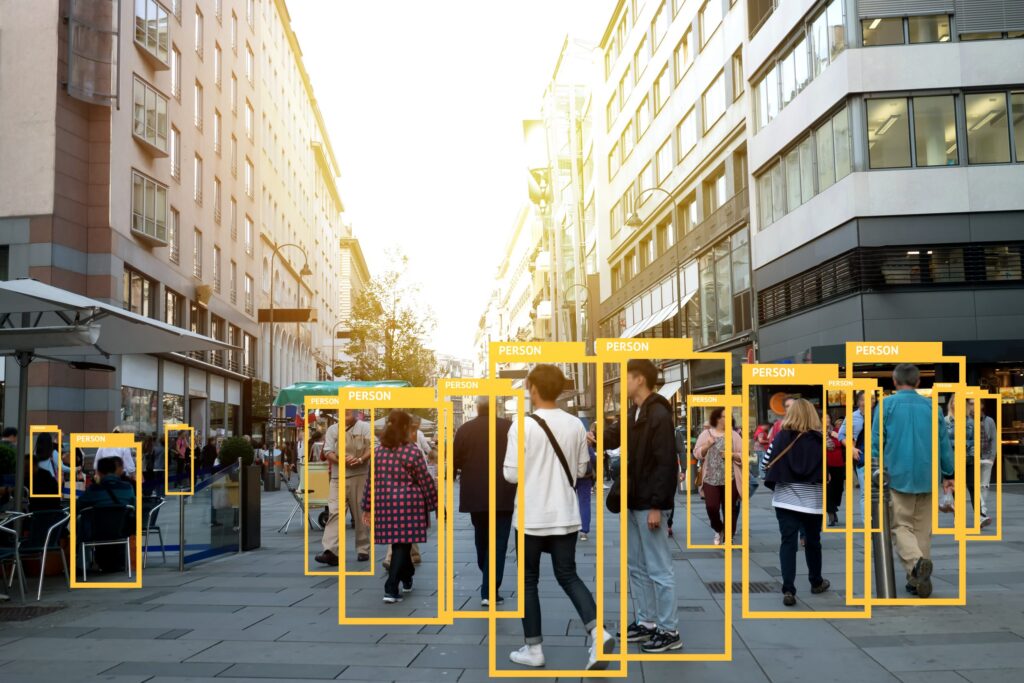
Beyond premium services, the API also let Sarda access the “server_get_user” endpoint & enumerate Bumble’s worldwide users. She was even able to retrieve users’ Facebook data & the “wish” data from Bumble, which tells the type of match they are searching for. The “profile” fields were also accessible, which contain personal information like political leanings, astrological signs, education, & even height & weight.
She reported that the vulnerability could also let an attacker to work out if a given user has the mobile app installed, & if they are from the same city, & worryingly, their distance away in miles.
Facial Machine-Learning
“This is a breach of user privacy as specific users can be targeted, user data can be commodified or used as training sets for facial machine-learning models, & attackers can use triangulation to detect a specific user’s general whereabouts,” Sarda stated. “Revealing a user’s sexual orientation & other profile information can also have real-life consequences.”
Sarda also confided that during her testing, she was able to see whether someone had been identified by Bumble as “hot” or not but found something curious.
“I still have not found anyone Bumble thinks is hot,” she commented.
API Vuln
Sarda observed that she and her team at ISE reported their findings ‘privately’ to Bumble to try to mitigate vulnerabilities prior to going public.
“After 225 days of silence from the company, we moved on to the plan of publishing the research,” Sarda outlined. “Only once we started talking about publishing, we received an email from Hacker One on 11/11/20 about how ‘Bumble are keen to avoid any details being disclosed to the press.’”
Hacker One then moved to put right some the issues, Sarda related, but not all. Sarda found when she re-tested that Bumble no longer uses sequential user IDs & updated its encryption.
User Base
“This means that I cannot dump Bumble’s entire user base anymore,” she observed.
Also, the API request that at one time gave distance in miles to another user is no longer working. However, access to other information from Facebook is still available. Sarda commented she expects Bumble will fix those issues to in the coming days.
“We saw that the Hacker One report #834930 was resolved (4.3 – medium severity) & Bumble offered a $500 bounty,” she explained. “We did not accept this bounty, since our goal is to help Bumble completely resolve all their issues by conducting mitigation testing.”
Sarda explained that she re-tested in Nov. 1 & all of the issues were still in place. As of Nov. 11, “certain issues had been partially mitigated.” She added that this shows Bumble was not responsive enough through their vulnerability disclosure program (VDP).
Disclosure
Not so, says Hacker One.
“Vulnerability disclosure is a vital part of any organisation’s security posture,” Hacker One outlined. “Ensuring vulnerabilities are in the hands of the people that can fix them is essential to protecting critical information.
Bumble has a history of collaboration with the hacker community through its bug-bounty program on Hacker One. While the issue reported on Hacker One was resolved by Bumble’s security team, the information revealed to the public includes information greatly exceeding what was responsibly disclosed to them at 1st.
Bumble’s security team works 24-7 to ensure all security-related issues are resolved swiftly & confirmed that no user data was compromised.”
Speed & Flexibility
APIs are an ‘overlooked’ attack vector, & are increasingly being used by developers, according to Jason Kent, Hacker-in-Residence for Cequence Security.
“API use has exploded for both developers & bad actors,” Kent explained. “The same developer benefits of speed & flexibility are leveraged to execute an attack resulting in fraud & data loss.
Human Error
In many cases, the root cause of the incident is human error, such as verbose error messages or improperly configured access control & authentication. The list goes on.”
Kent added that the responsibility is on security teams, & API Centres of Excellence, to work out how to improve their security.
Bumble is sadly not alone. Similar dating apps like OKCupid & Match have also had issues with data privacy vulnerabilities over the years.
https://www.cybernewsgroup.co.uk/virtual-conference-january-2021/